Here are a few common questions and answers that we’ve found users pose when they need security help. As always, we welcome your questions when posed via the [U]Tech Service Desk at help.case.edu.
In the event a computer is lost or stolen at CWRU, it is important to first contact Campus Police at 216.368.3333. They will assist in filing a police report and in attempting to locate the stolen device. If the computer is a machine owned by CWRU, the faculty or staff member will need to speak to their supervisor to ensure that a replacement machine is ordered.
For student and personal machines, the device owner bears the responsibility of ordering a replacement. Discounts on computers are offered through eStore.
If you work with research in the Secure Research Environment, contact the [U]Tech Service Desk at help@case.edu and indicate that your computer was stolen and you are an SRE user.
Contact us at infosec@case.edu We can provide brief or extended trainings on information security from the handling of restricted information to basic and intermediate technical cyber safety education.
- Securing your computer is an important step in preventing intruders from stealing valuable information stored, such as credit card and bank information as well as ID and password data. In addition, some thieves can also access your computer's resources such as hard disk space, your processor and your Internet connection.
- More than 90% of computer compromises are due to fraudulent email campaigns, where users click on nefarious links.
- There are steps that you can take to safeguard your device such as choosing smart passwords, backing up your work, and installing anti-virus programs, firewalls and encryption programs.
- Go to Information Security for more assistance on keeping your computer safe. You can also try OnGuard Online at https://www.consumer.ftc.gov/features/feature-0038-onguardonline.
How to recognize Phish
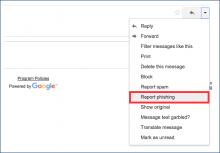
In the event that you receive a message fitting this description, please report the phishing email to Google by clicking the down arrow to the right of the reply button in webmail, then select "Report phishing"
Phishing emails can also be forwarded to security@case.edu.
If you clicked the link in the email and entered your CWRU account credentials, please change your password immediately and/or call the [U]Tech Service Desk at 216.368.HELP if you need assistance changing your password.
Awareness Training
Securing your technology doesn’t have to be difficult. Consider safe computing options:
- I clicked on a link in an email and I think it was a scam (Please view Phishing examples here)
- I need to change my password (https://its-services.case.edu/my-case-identity/password/change/)
- I got a strange email and I’m not sure that it’s real (forward email to help@case.edu requesting review or assistance)
- I think I’ve been hacked; my contacts are emailing me to say that I’m sending them emails that I never sent? (forward email to help@case.edu requesting review or assistance)
- My CWRU owned computer was stolen -Report the theft to the CWRU Police Department 216.368.3300
If you had restricted information (eg: patient or research information), also contact help@case.edu.
- I have research with patient information. How do I protected it? (email help@case.edu requesting Information Security Assistance)
- I need a data management or data security plan for my grant proposal and/or IRB. (email help@case.edu requesting Information Security Assistance)
Quick Tips for Long Lasting Safety
Your university password guards your entire digital life at Case Western Reserve University. Never share it with others—even friends and family members. Additionally, university departments will never ask you for your password. Emails requesting this information from you are fraudulent and should be deleted.
Your mobile device contains information about you, as well as your friends and family. Don’t let this information fall into the wrong hands. Employ the passcode or lock screen pattern option on your smartphone to ensure only you can access its data. The longer the passcode or pattern, the more secure your phone will be in the event it is lost or stolen. Learn how to secure your mobile phone.
The Case Western Reserve Acceptable Use Policy requires that antivirus software be installed and used on all computers at the university. Download Symantec™ Endpoint Protection for free via the Software Center.
Installing browser plugins is a popular way to extend the functionality of your favorite Web browser. WARNING: when these tools become out of date, they leave the device vulnerable to online attacks. In fact, many malware infections are a direct result of out-of-date browser plugins. Use Qualys® BrowserCheck to check your Web browser for updates and to find outdated plugins.
Use Spirion™ to find, protect or eradicate any sensitive information that may exist on your computer, such as credit card and social security numbers. Download it for free via the Software Center.
(“Phishing: What to do") and learn how to recognize a fraudulent attempt to compromise your credentials. If you receive a suspicious email, forward it to help@case.edu and the Information Security Office can remove access to the fraudulent site, protecting your system and the rest of our community.
Case Western Reserve incorporated two-factor authentication into the Virtual Private Network (VPN) and some Single Sign On (SSO) authenticated applications. Two-factor authentication provides added security by prompting you for a unique code in addition to your password. Learn More at our Duo Information site.